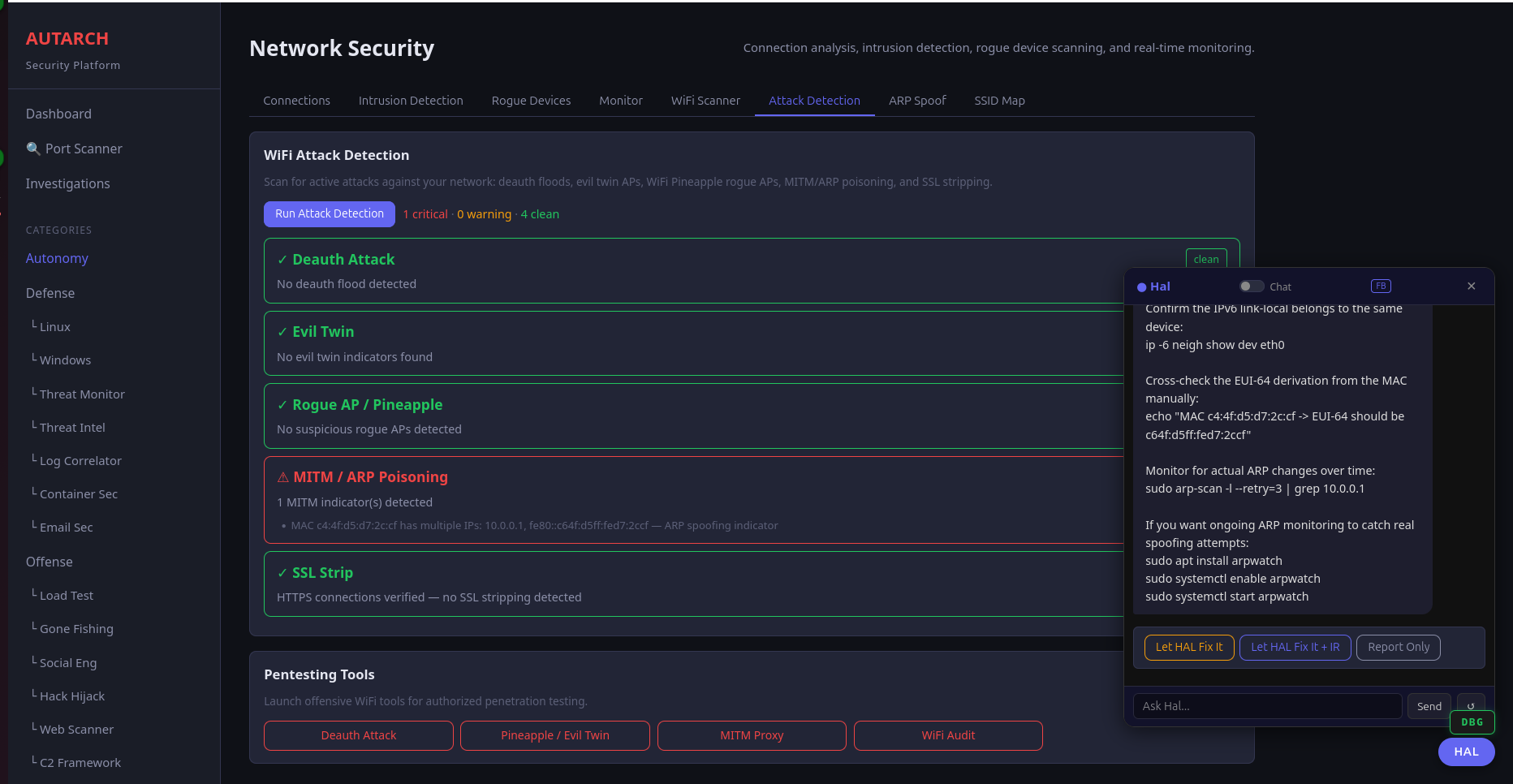
WiFi Attack Detection
Real-time detection of deauthentication attacks, evil twins, rogue access points, ARP poisoning, MITM attacks, and SSL stripping. Every threat is identified, categorized, and explained with actionable remediation steps — automatically analyzed by Agent HAL.
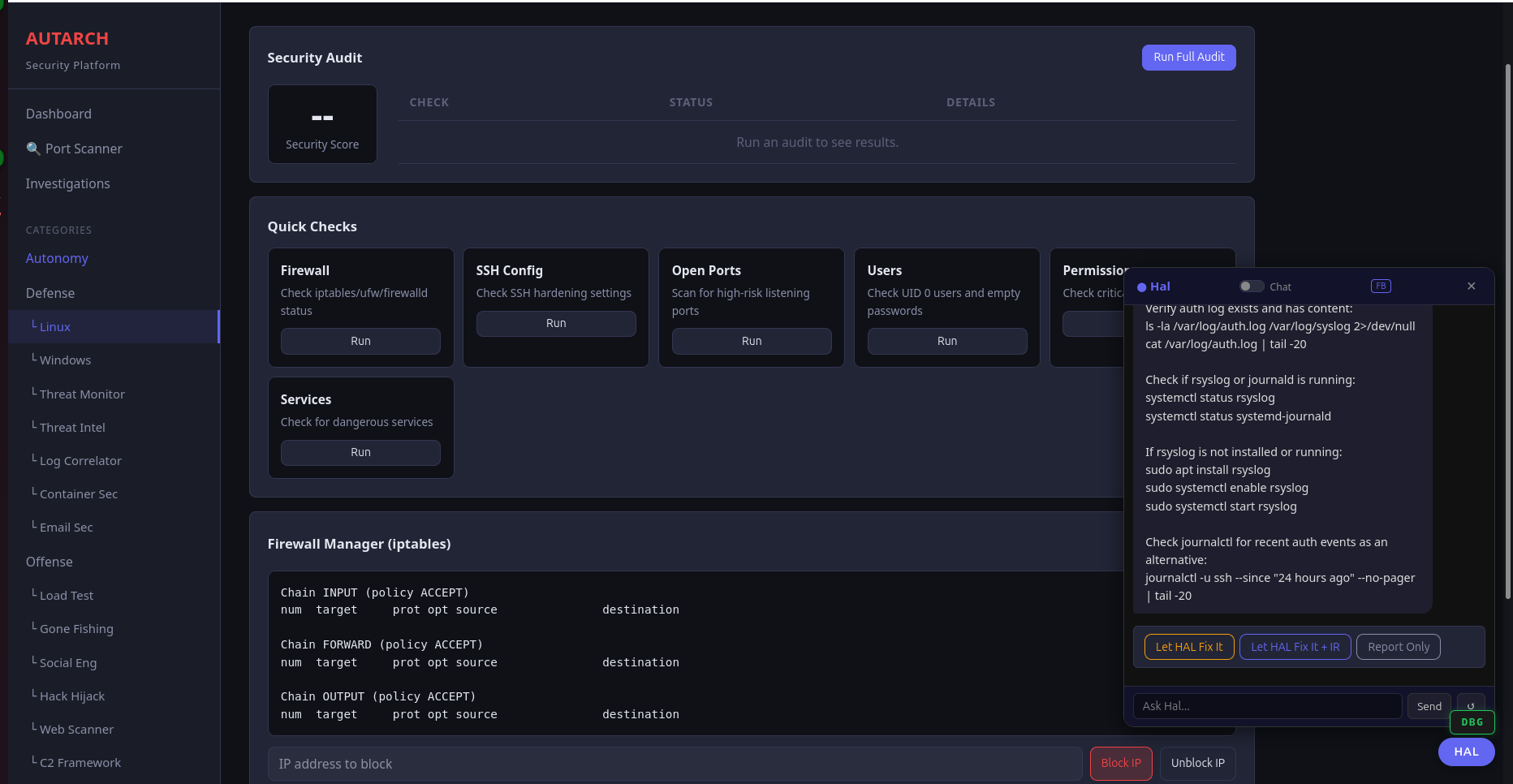
System Hardening
One-click security audits across firewall configuration, SSH hardening, open port analysis, user permissions, dangerous services, and firewall rule management. Results are scored, prioritized, and paired with fix commands you can run directly.
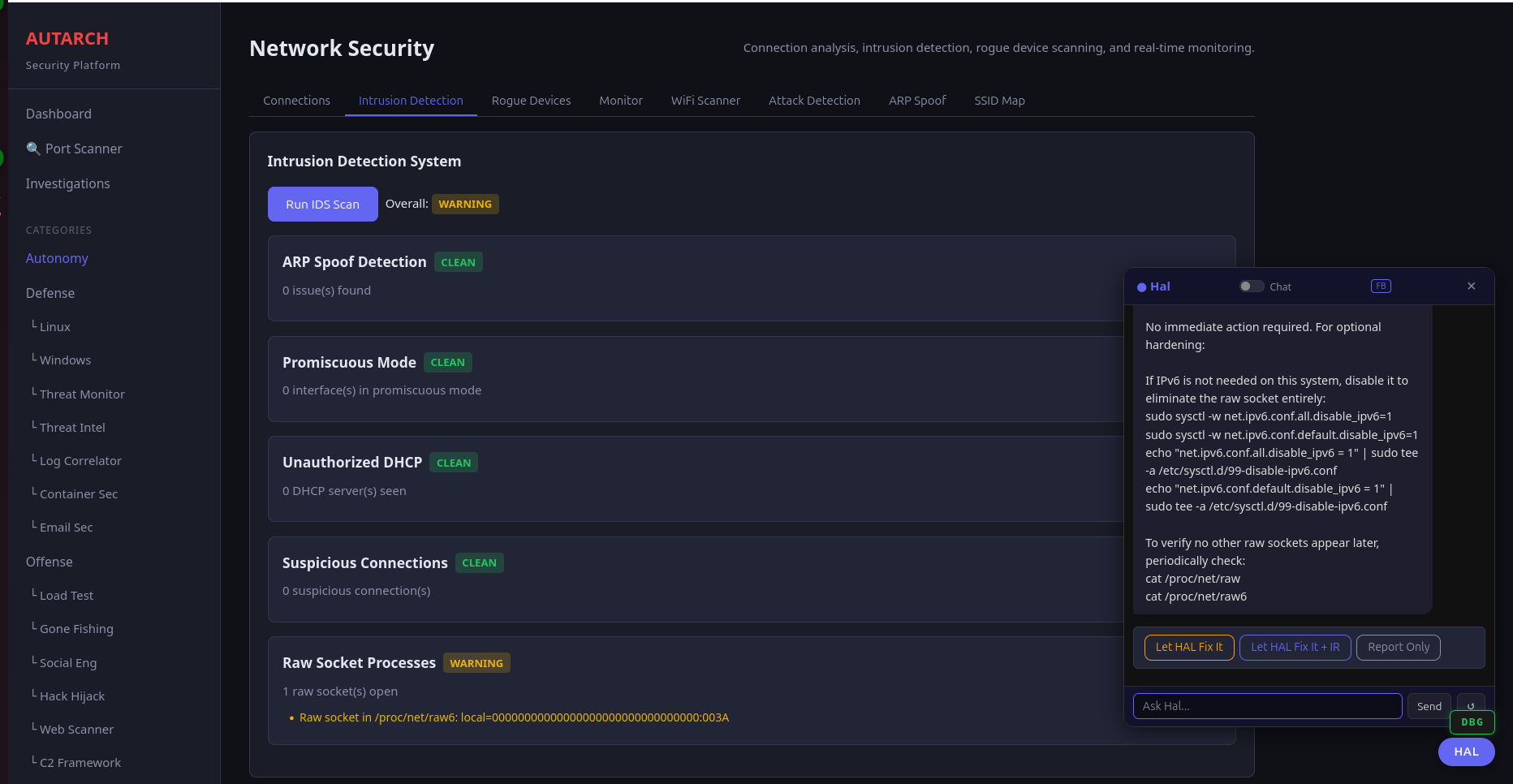
Threat Monitoring
ARP spoof detection, promiscuous mode monitoring, unauthorized DHCP servers, suspicious connections, and rogue socket processes — all monitored continuously. The HAL Auto-Analyst provides real-time risk assessments and response recommendations.